Kernel Panic or Keen Insight






Quiz Complete!
Kernel Panic or Keen Insight: The Hidden Rules That Keep Computers Honest

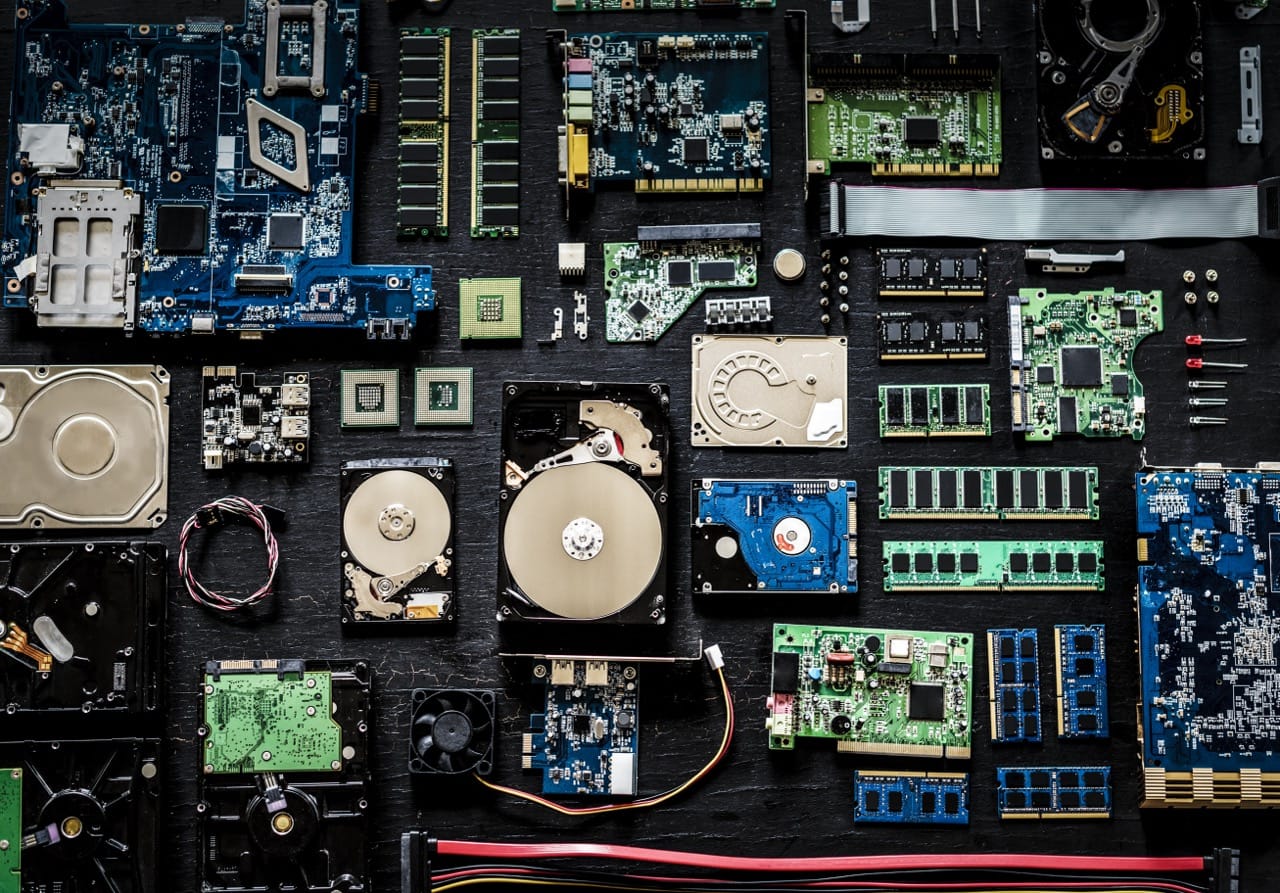
Most people meet computers through apps and devices, but the real drama happens underneath, where an operating system brokers peace between impatient programs and limited hardware. When you see a kernel panic or a blue screen, it is often the system choosing to stop rather than continue in a corrupted state. The kernel sits at the center of this bargain: it schedules CPU time, manages memory, talks to devices, and enforces protection boundaries so one process cannot casually scribble over another. Those boundaries are not just policy; they are built into hardware features like privilege levels, page tables, and interrupts.
Virtual memory is one of the most important tricks in modern computing, and it is easy to misunderstand. It does not magically make RAM infinite. Instead, it gives each process the illusion of a large, private, contiguous address space and maps those virtual addresses to physical memory as needed. Page faults are not always errors; they are how the system lazily loads data and moves less used pages to disk. This indirection also enables safety: if a program touches an address it does not own, the hardware raises a fault and the OS can terminate it cleanly. The cost is complexity and performance risk. Thrashing happens when the working set no longer fits and the system spends more time swapping pages than doing useful work.
Caches add another layer of illusion. A CPU cache can make memory feel fast, but it cannot guarantee freshness unless the coherence protocol and memory model line up with your assumptions. On multicore systems, each core may have its own cache, and keeping them consistent requires protocols such as MESI, which track whether a cache line is modified, exclusive, shared, or invalid. Even with coherence, the order in which writes become visible to other cores can be surprising. That is why race conditions can appear or disappear depending on timing, compiler optimizations, or CPU architecture. A common debugging lesson is that adding logging can “fix” a bug by changing the schedule. Correctness requires synchronization primitives like mutexes, semaphores, atomics, and memory barriers, which tell both the compiler and the CPU what reordering is forbidden.
Endianness is another detail that stays hidden until it breaks something. It describes byte order in multi byte values. Network protocols traditionally use big endian, often called network byte order, while many popular CPUs are little endian. Modern software usually converts explicitly, but file formats, binary protocols, and low level debugging still reward knowing what you are looking at.
Networking feels like magic until you learn the quiet rules that keep it working. IP routing moves packets across networks without guaranteeing delivery. TCP adds reliability with sequence numbers, acknowledgments, retransmission, and congestion control. Checksums help detect corruption, but they are not security and they are not perfect. Ethernet CRCs are strong at catching random errors, yet they cannot stop intentional tampering. For that you need cryptography and authentication, which is where TLS comes in. TLS did not just make web browsing safer; it changed how systems are designed by making encryption the default expectation for APIs, services, and even internal traffic.
Wi Fi is another place where standards quietly shape daily life. The 802.11 family has evolved through changes in modulation, channel width, and multiple input multiple output antennas. Security evolved too, from the broken WEP to WPA2 and WPA3. Many real world failures come from configuration, not math: weak passwords, outdated devices, and insecure fallback modes.
A lot of computer history is really the history of tradeoffs. RISC and CISC debates, the rise of UNIX ideas like “everything is a file,” and the shift from single fast cores to many cores all left fingerprints on today’s systems. If you have ever trusted a cache, blamed the network, or chased a heisenbug at 2 a.m., you have already met the themes of this quiz: computers are deterministic machines that behave unpredictably when you ignore the layers of rules that make them work.